Unlocking Efficiency: Identifying Business Processes for Optimization Through Digital Transformation
In the modern business landscape, efficiency is key.
Companies are constantly seeking ways to streamline operations and improve performance.
One strategy that has gained significant traction is business process optimization. This approach focuses on refining existing business processes to increase efficiency and effectiveness.

But how do you identify which processes need optimization? And how can digital transformation aid in this endeavor?
This article aims to answer these questions. It will provide insights into the role of digital transformation in business process optimization and how to identify processes ripe for improvement.
Whether you’re a business owner, operations manager, or a process improvement specialist, you’ll find valuable information to help you unlock efficiency in your organization.
The Imperative for Business Process Optimization
In today’s competitive business environment, optimization is not just an option. It’s a necessity.
Business process optimization involves analyzing your current processes, identifying areas of inefficiency, and making necessary improvements.
The goal is to reduce waste, eliminate redundancies, and streamline workflows. This can lead to significant cost savings and improved customer satisfaction.
In essence, business process optimization is about doing more with less. It’s about maximizing your resources to deliver better results.
Digital Transformation as a Catalyst for Optimization
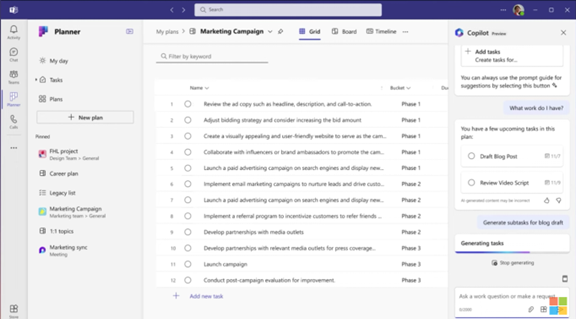
Digital transformation is a powerful catalyst for business process optimization. It involves leveraging technology to improve business operations and customer experiences.
By digitizing manual processes, businesses can reduce errors and increase efficiency. Automation can free up employees’ time, allowing them to focus on more strategic tasks.
Moreover, digital transformation enables data-driven decision-making. With the right tools, businesses can collect and analyze data to identify trends, monitor performance, and make informed decisions.
In short, digital transformation can unlock new levels of efficiency and effectiveness in your business processes. It’s a key enabler of optimization.
Identifying Processes Ripe for Optimization
Identifying which processes to optimize can be a daunting task. However, there are certain signs that a process might be ripe for optimization.
Processes that are time-consuming, error-prone, or causing customer complaints are often prime candidates. Similarly, processes that rely heavily on manual work or outdated technology can often be improved through digital transformation.
Here are some steps to identify processes for optimization:
- Map out your current processes.
- Identify pain points and bottlenecks.
- Prioritize processes based on their impact on your business goals.
- Consider the feasibility of optimizing each process.
- Seek feedback from employees and customers.
The Role of Business Process Optimization Consulting
Business process optimization consulting plays a crucial role in the optimization journey. These consultants bring expertise and an outside perspective that can be invaluable.
They can help identify inefficiencies that internal teams might overlook. They also bring knowledge of best practices and the latest technologies that can aid in process optimization.
Moreover, consultants can provide training and support to ensure the sustainability of optimized processes. They can also help build a business case for process optimization initiatives, demonstrating the potential return on investment.
Key Benefits of Optimizing Your Business Processes
Optimizing your business processes can yield significant benefits. One of the most notable is cost reduction. By streamlining workflows and eliminating redundancies, businesses can save substantial resources.
Improved customer satisfaction is another key benefit. Efficient processes lead to faster response times and better service, enhancing the customer experience.
Optimized processes also increase competitiveness. They enable businesses to adapt quickly to market changes and seize new opportunities.
Finally, process optimization can drive innovation. It encourages a culture of continuous improvement, fostering creativity and problem-solving. This can lead to the development of new products, services, or business models.
Strategies for Effective Process Improvement
Effective process improvement requires a strategic approach. One key strategy is aligning process optimization with organizational goals. This ensures that improvements contribute to the overall business objectives.
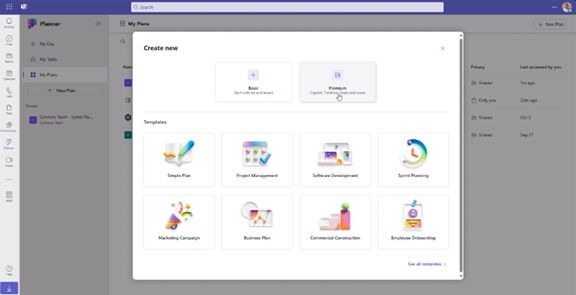
Another strategy is leveraging technology. Digital tools can automate routine tasks, streamline workflows, and reduce errors. They can also provide valuable data for performance measurement and decision-making.
Here are some strategies for effective process improvement:
- Align process optimization with organizational goals
- Leverage technology to streamline workflows and reduce errors
- Use data to measure performance and guide decision-making
- Engage employees in the process improvement efforts
Employee engagement is also crucial. Employees who are involved in process improvement efforts are more likely to embrace changes and contribute innovative ideas.
Overcoming Common Challenges in Process Optimization
Process optimization can present several challenges. One common challenge is resistance to change. Employees may be hesitant to adopt new processes, especially if they are comfortable with the old ways of doing things.
Another challenge is the lack of clear, measurable goals. Without these, it can be difficult to gauge the success of optimization efforts. It’s important to set specific, achievable targets for process improvement.
Finally, maintaining optimized processes can be a challenge. It requires ongoing monitoring and adjustment to ensure that processes remain efficient and effective. This is where the concept of continuous improvement comes into play.
Case Studies: Success Stories of Process Optimization
Let’s look at some real-world examples of successful process optimization. A global manufacturing company, for instance, used digital transformation to streamline its supply chain processes. This led to a significant reduction in lead times and improved customer satisfaction.
In another case, a financial services firm used data analytics to identify inefficiencies in its loan approval process. By automating certain steps, the firm was able to reduce approval times and increase the number of loans processed.
These examples highlight the potential of process optimization to drive tangible improvements in efficiency and customer service.
Tools and Technologies Driving Process Optimization
The digital age has brought a plethora of tools and technologies that can aid in process optimization. Software platforms for process mapping and analysis, for instance, can provide valuable insights into where inefficiencies lie.
Automation technologies, such as Robotic Process Automation (RPA), can take over repetitive tasks, freeing up human resources for more strategic work. Meanwhile, data analytics tools can help organizations measure process performance and identify areas for improvement.
Artificial intelligence and machine learning also hold great promise. These technologies can analyze large volumes of data to identify patterns and predict future outcomes, further enhancing the optimization process.
Maintaining and Scaling Optimized Processes
Once processes have been optimized, it’s crucial to maintain their efficiency. Regular monitoring and analysis can help ensure that processes continue to perform at their best.
Scalability is another important consideration. As your business grows, your processes should be able to adapt and expand to meet increasing demands.
Finally, continuous improvement should be a key part of your strategy. Even the most optimized processes can often be improved further.
Conclusion: The Continuous Journey of Business Process Optimization
Business process optimization is not a one-time task. It’s a continuous journey that requires ongoing effort and commitment.
As market conditions and technologies evolve, businesses must be ready to adapt their processes accordingly. This ensures that they remain competitive and efficient.
In conclusion, by identifying processes for optimization and leveraging digital transformation, businesses can unlock significant efficiency gains. This journey, while challenging, can lead to improved performance, cost savings, and a stronger competitive position.